38 security labels access control
Mandatory access control - Wikipedia Access to the labels and control mechanisms are not [citation needed] robustly protected from corruption in protected domain maintained by a kernel. The applications a user runs are combined with the security label at which the user works in the session. Access to information, programs and devices are only weakly controlled [citation needed]. Security Labels Overview Uniquely configured by each site, security labels work with the Windchill access control policies and ad hoc permissions for an object to determine whether a user is authorized to access an object. A site can configure multiple security labels to cover various needs, such as identifying legal information, establishing export control criteria, or protecting proprietary information.
8 Access Control Models - Strengths, Weaknesses, and More Under mandatory access control (MAC), security administrators set access labels for both users and objects. Mandatory access control is the most secure of the major access control models, and also the most demanding to maintain.

Security labels access control
Security: Access Control Getting a connection error when accessing the AEC webpage When trying to access the Access Easy Controller via Microsoft Edge, Chrome or other web browsers, you may get an error, "the connection for this site is not secure", which prevents you from connecting to the AEC. No ratings 113 0 03-30-2022 Can I downgrade my AEC firmware to 2.1.8.5? Setting Access Control Permissions for Agreement Managers Specialized Administration > Ensuring Data Security > Security Labels and Agreements > Configuring Security Labels > Additional Security Label Configuration Concerns > Setting Access Control Permissions for Agreement Managers . ... For agreement managers to access and modify agreements, the appropriate access control rules must be set. non-discretionary access control - Glossary | CSRC A means of restricting access to objects based on the sensitivity (as represented by a security label) of the information contained in the objects and the formal authorization (i.e., clearance, formal access approvals, and need-to-know) of subjects to access information of such sensitivity. Mandatory Access Control is a type of nondiscretionary ...
Security labels access control. Access Control Models - UHWO Cyber Security MAC uses "security labels" to assign resource objects on a system. There are two pieces of information connected to these security labels: classification (high, medium, low) and category (specific department or project - provides "need to know"). Each user account is also assigned classification and category properties. Access Control using Security Labels & Security Clearance Security Labels and Security Clearance provides a mechanism for controlling access to information that works well for large numbers of users. It can be an effective approach for access control in organizations that do not use non-electronic security labels. The following diagram shows the translation of the earlier example into electronic form. Sensitivity labels for Microsoft Teams - Microsoft Teams ... A team owner can change the sensitivity label and the privacy setting of the team at any time by going to the team, and then click Edit team. Control guest access to teams. You can use sensitivity labels to control guest access to your teams. Teams created with a label that doesn't allow guest access are only available to users in your ... Label-based access control (LBAC) overview Label-based access control (LBAC) greatly increases the control you have over who can access your data. LBAC lets you decide exactly who has write access and who has read access to individual rows and individual columns. What LBAC does The LBAC capability is very configurable and can be tailored to match your particular security environment.
Label Security - Oracle Oracle Label Security uses row level data classifications to enforce access controls restricting users to only the data they are allowed to access. It enables organizations to control their operational and storage costs by enabling data with different levels of sensitivity to co-mingle within the same database. Mandatory Access Control: How It Works Mandatory access control relies on a system of security labels. Every resource under MAC has a security classification, such as Classified, Secret, and Top Secret. Likewise, every user has one or more security clearances. To access a given resource, the user must have a clearance matching or exceeding the resource's classification. Google Workspace Updates: Security groups help manage ... Security groups help you easily regulate, audit, and monitor groups used for permission and access control purposes. They enable admins to: Apply a label to any existing Google Group to distinguish it from email-list groups. Mandatory Access Control - an overview | ScienceDirect Topics Mandatory Access Control ( MAC) is system-enforced access control based on subject's clearance and object's labels. Subjects and objects have clearances and labels, respectively, such as confidential, secret, and top secret. A subject may access an object only if the subject's clearance is equal to or greater than the object's label.
Security-labels - FHIR v4.0.1 A security label is a concept attached to a resource or bundle that provides specific security metadata about the information it is fixed to. The Access Control decision engine uses the security label together with any provenance resources associated with the resource and other metadata (e.g. the resource type, resource contents, etc.) to mandatory access control (MAC) - Glossary | CSRC NIST SP 800-53 Rev. 5 under mandatory access control A means of restricting access to objects based on the sensitivity (as represented by a security label) of the information contained in the objects and the formal authorization (i.e., clearance, formal access approvals, and need-to-know) of subjects to access information of such sensitivity. Computer access control - Wikipedia In computer security, general access control includes identification, authorization, authentication, access approval, and audit.A more narrow definition of access control would cover only access approval, whereby the system makes a decision to grant or reject an access request from an already authenticated subject, based on what the subject is authorized to access. en.wikipedia.org › wiki › Access_controlAccess control - Wikipedia In the fields of physical security and information security, access control (AC) is the selective restriction of access to a place or other resource, while access management describes the process.The act of accessing may mean consuming, entering, or using. Permission to access a resource is called authorization.. Locks and login credentials are two analogous mechanisms of access control.
3 Types Of Access Control Systems And How To Choose The ... Mandatory Access Control is a security model more commonly used in organizations that require a high level of confidentiality and classification of data - such as government offices and military institutions. In MAC, owners do not have a say in the entities having access to a unit or facility, instead, access rights are regulated by a central ...
3.3: Access Control - Models - Engineering LibreTexts A Mandatory Access Control system implements a simple form of rule-based access control to determine whether access should be granted or denied by matching: An object's sensitivity label; A subject's sensitivity label; Lattice-based access control: These can be used for complex access control decisions involving multiple objects and/or subjects ...
Security labels Configuring Label-Based Access Control The general procedure involves a few SQL-based tasks that define precise but flexible database security objects. How security labels control access Security labels rely on security label components to store information about the classification of data and about which users have access authority.
How security labels control access Security labels rely on security label components to store information about the classification of data and about which users have access authority. Label-based access control (LBAC) works by comparing the labels that you have associated with users against labels that you have associated
Security Labels and Mandatory Access Control (MAC) Security Labels and Mandatory Access Control (MAC) Mandatory Access Control (MAC) is a security policy that governs which subjects can access which objects, and in what way, based upon certain rules. These rules are the "*-property" and the "simple security property." RACF commands are used to manage MAC for CP commands, DIAGNOSE
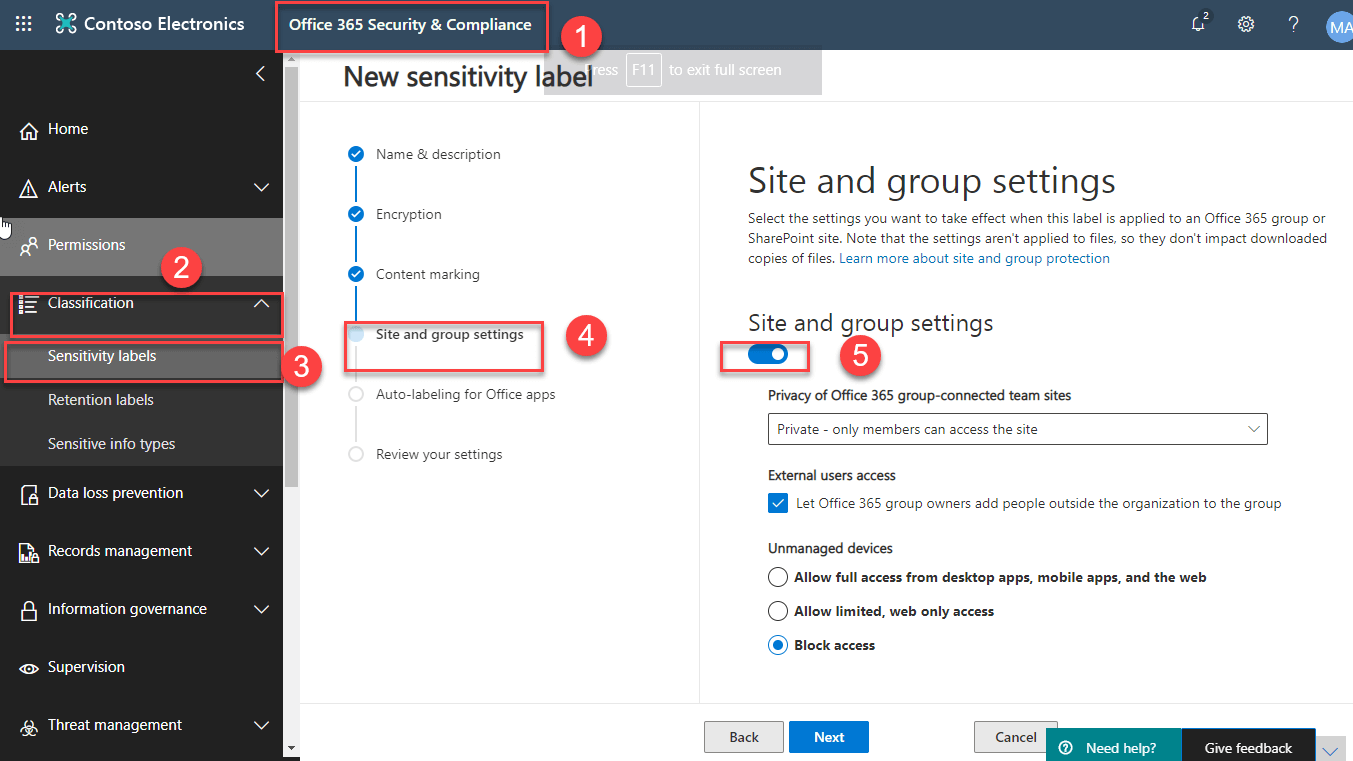
Overview of security and compliance - Microsoft Teams ... Apr 21, 2022 · Sensitivity labels. Apply sensitivity labels to protect and regulate access to sensitive organizational content created during collaboration within teams. For example, apply labels that configure the privacy (public or private) of teams, control guest access and external sharing, and manage access from unmanaged devices.
Access Control Models - CompTIA Security+ SY0-501 - 4.3 ... But it's also a very weak form of access control security because it relies on the owner of the file to be setting the proper security for that particular object. Role-based access control, or RBAC, is a much broader form of control that's based on your particular role in the organization.
Security - FHIR v4.0.1 These Resources will often use the security labels to differentiate various confidentiality levels within this broad group of Patient Sensitive data. Access to these Resources often requires a declared Purpose Of Use. Access to these Resources is often controlled by a Privacy Consent . See the section below on Authorization and Access Control .


Post a Comment for "38 security labels access control"